Used, not useless: Data on second-hand devices creates a cybersecurity concern for businesses

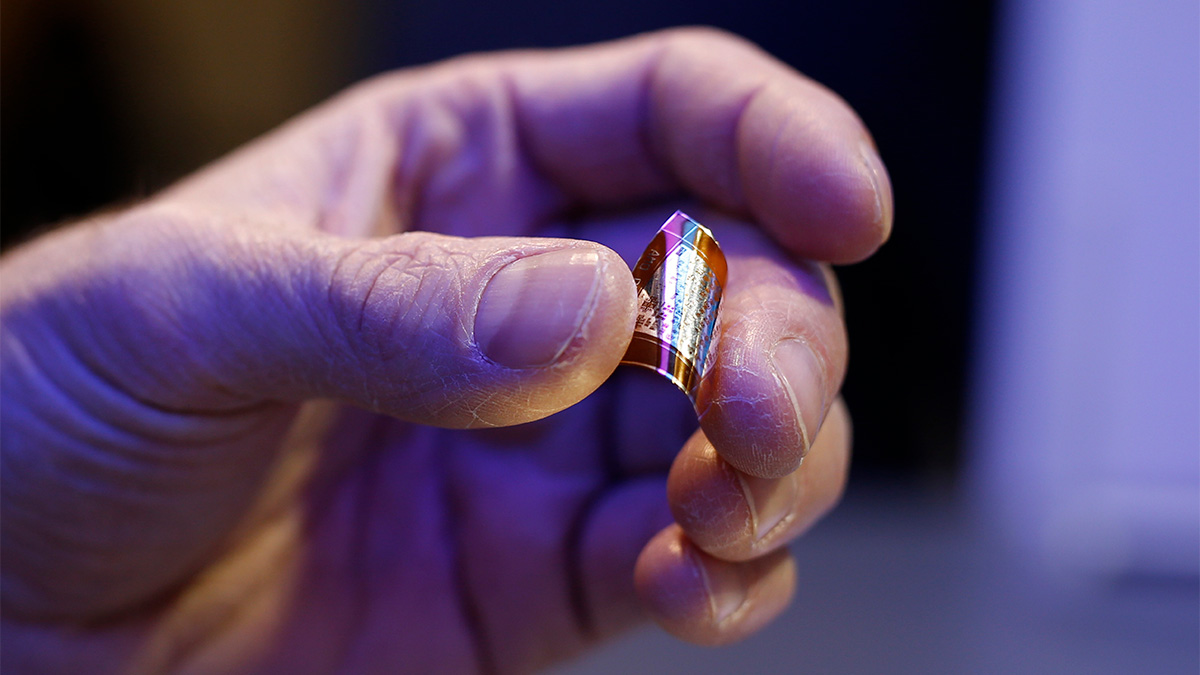
As many as 90% of second-hand storage media devices such as USB sticks and hard drives contain traces of private and business data from previous owners, according to research conducted by Kaspersky. Private photos and videos, pornographic content, and intimate messages have been found to exist alongside banking documents, medical reports, contact details, company emails, and much more, putting former owners and their employers at risk.
The cybersecurity expert’s Global Research & Analysis Team (GReAT) made this discovery during an exercise where they gathered 185 storage media devices to assess the security ramifications of second-hand ownership. The resultant threat to consumers and enterprises alike was found to be stark, as only 11% of all analysed storage device memories were entirely clean. Almost one-fifth contained data that could be discovered and extracted immediately, while a staggering 74% held data that could still be recovered through file carving.
The concerning results complement an additional study conducted by Kaspersky, where company data, login details, passports, personal content, and a host of correlating data were all reported by purchasers of second-hand desktop computers, laptops, smartphones, and storage media. This study was carried out across 2,000 UK, 1,000 German, and 500 Austrian respondents. And while the sample may have been European-based, the results reflect a global cybersecurity challenge, given that they are sold second-hand.
Of the 2,000 UK consumers, 649 had bought a used computer, 802 had a mobile device, and 321 had purchased used storage media. Among the former, 13% found existing contact details for the previous owner, 10% found business-related data from organisations, and another 10% found official documentation such as passports and driving licenses. Similar percentages were found across mobile devices, USB sticks, and hard drives, with an additional concern of up to 13% of computers also containing documents that listed passwords and login details of former owners.
The vulnerability of this data was compounded as respondents revealed what they would do with this information should they find it. As many as 41% admitted they would take action with the data, including uploading or saving the data, posting interesting or embarrassing data on social media, and showing the information to family and friends.
The link between consumer handling of second-hand devices and business vulnerability becomes even more clear when gauging the number of transactions involving used devices. A quarter of consumers have bought a used laptop while 15% have purchased a second-hand desktop. Almost a fifth have bought a used tablet, while a third have procured a used smartphone, and one in six (16%) have bought a used storage media device. Furthermore – poignantly, as we enter the festive period – 26% have been gifted used computers and mobile devices with a previous user’s data still on them.
This is not a trend that will dissipate any time soon, and the issue needs to be combated at the source.
Businesses should encourage employees to wipe clean devices before selling or passing them on if they’re using personal devices for work purposes – though ideally, corporate data should never be stored on non-corporate devices.
Tips to ensure devices are clean include:
Mobile
- Back up all data, including contacts.
- Remove the SIM card and any external storage such as a microSD card.
- Log out of services like email and social media, then clear the data from these apps if you can.
- Factory reset the device.
Laptop computer
Use a secure erase feature as a simple delete is not enough.
Deleting data using File Shredder
When “normally” deleting via the Del key followed by emptying the Recycle Bin, the files are not deleted properly, but only the reference to their location on the disk is removed. To shred files, there are dedicated programs. Some security solutions such as Kaspersky Total Security have such file shredders directly integrated.
Deleting Cipher data with on-board tools
Files or directories can be deleted quite reliably with Windows’ own onboard tool “Cipher”. The tool is actually used to encrypt files but can also delete them from the hard disk or render them unusable. Using the Windows tool is particularly useful if no additional programs are to be downloaded to delete data.
Meanwhile, purchasers should always activate security software for testing, and perform a scan immediately after purchase and before using the device for the first time. These steps should form an extra layer of caution on top of an embedded solution that provides protection.
Marco Preuss, head of GReAT Europe said: “This experiment has highlighted the importance of encrypting confidential data on laptops, tablets, or smartphones; the potential damage if personal data falls into the wrong hands is enormous. Identity theft, access to accounts, blackmail, or even social ruin of the original owners would be possible. In addition, data could be used to carry out attacks on the previous owner of the device as well as close family, friends or peers.”
Christian Funk, head of GReAT DACH said: “Only a complete overwriting of the actual information on a data carrier can remedy this. The criticality of sensitive, personal data seldom loses its effectiveness over time, even if the collection itself is far in the past.”